Critical cPanel & WHM Auth Bypass CVE-2026-41940 Was Exploited as a Zero-Day Since February — All Supported Versions Now Patched (April 28, 2026)
cPanel shipped emergency patches on April 28, 2026 for CVE-2026-41940, a CVSS 9.8 authentication bypass exploited in the wild since at least February. Every supported cPanel & WHM build is affected — operators should patch immediately and rotate credentials.
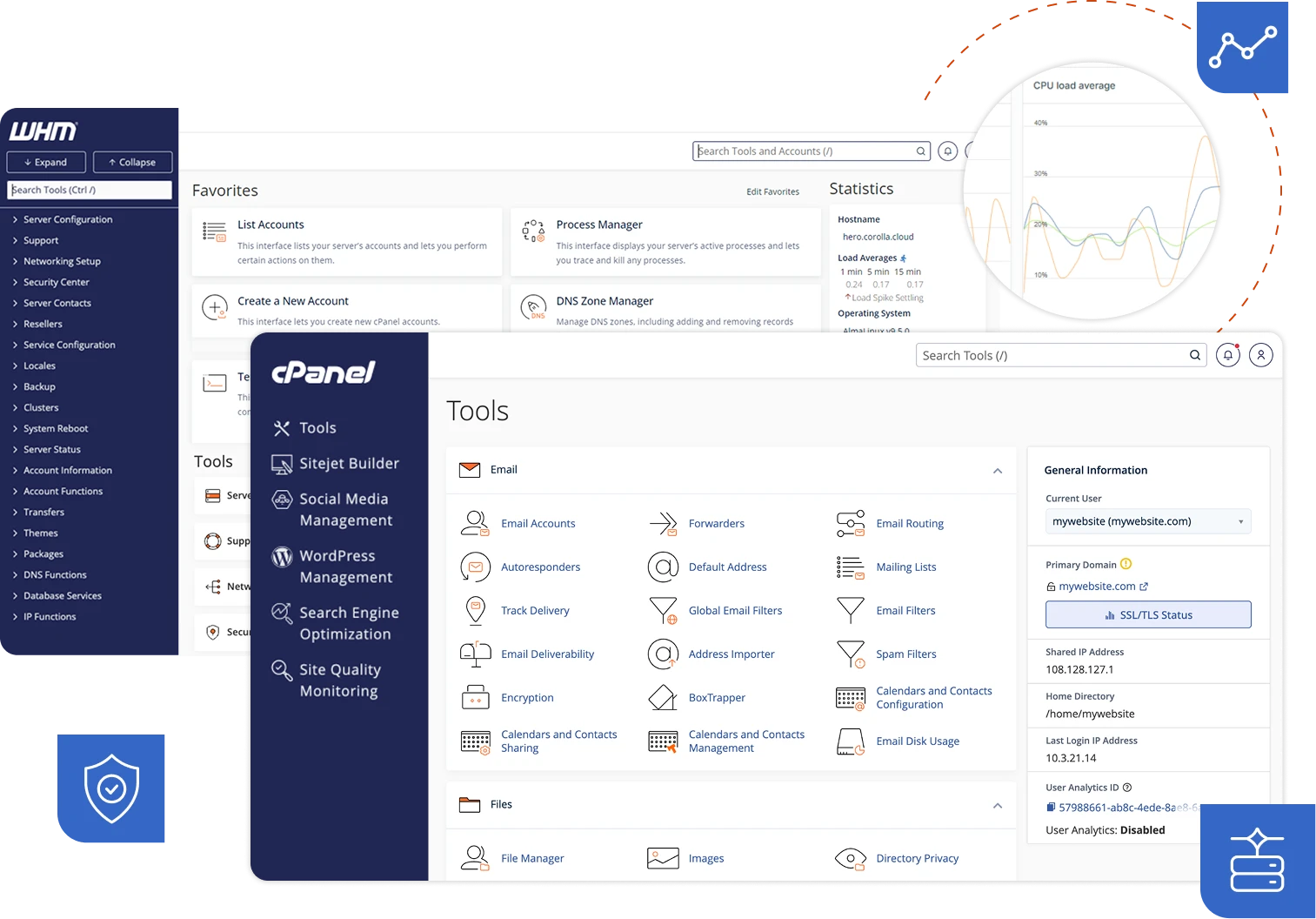
cPanel on released emergency patches for CVE-2026-41940, a critical authentication bypass that has been exploited as a zero-day since at least . The CVSS 9.8 flaw lets an unauthenticated attacker take over WHM with administrative access on every supported version of cPanel and WHM, including DNSOnly — software that, according to the vendor, manages roughly 70 million domains worldwide.
What Happened
The vulnerability, discovered and disclosed by watchTowr Labs, is a CRLF (Carriage Return Line Feed) injection flaw in cPanel’s session-handling code. An attacker first triggers a failed login to mint a pre-authentication session, then sends a crafted HTTP Basic Authorization header whose password field is stuffed with \r\n-separated fake session records. With the session cookie’s encryption key stripped, the injected records are written raw into the on-disk session file. A second deliberately-malformed request — missing its security token — forces cPanel to re-read the file and flush the attacker-controlled records into its JSON cache, granting a fully-authenticated administrative session.
The vendor first heard about the bug from watchTowr roughly two weeks before the public advisory and, according to multiple security publications, initially responded that nothing was wrong. Patched builds 11.110.0.97, 11.118.0.63, 11.126.0.54, 11.132.0.29, 11.134.0.20, 11.136.0.5, and WP Squared 11.136.1.7 shipped within hours of cPanel finally accepting the report on April 28. watchTowr published its full technical write-up and proof-of-concept the next day.
Key Details
- CVSS 9.8 (critical) — pre-authentication, network-reachable, no user interaction, full administrative impact on confidentiality, integrity, and availability.
- Exploited in the wild since February 23, 2026 per Imperva telemetry, with nearly 4,000 attack requests observed against monitored customer environments after public disclosure.
- Affects all supported versions of cPanel & WHM after 11.40, plus DNSOnly. Patched releases are 11.110.0.97, 11.118.0.63, 11.126.0.54, 11.132.0.29, 11.134.0.20, 11.136.0.5, and WP Squared 11.136.1.7.
- Root cause: CRLF injection in the login flow allows attacker-controlled data to be written verbatim into the on-disk session file and replayed as an authenticated session.
- CISA confirmed exploitation in a follow-up advisory on April 30, urging all hosting providers and cPanel operators to patch immediately.
What Developers and Users Are Saying
Reaction across the security community has been sharp. watchTowr’s own write-up — titled “The Internet Is Falling Down, Falling Down, Falling Down” — framed the disclosure as a near-disaster given cPanel’s footprint across shared hosts at GoDaddy, Bluehost, HostGator, A2 Hosting and dozens of smaller providers. Multiple commenters on r/sysadmin and r/webhosting noted that hosting companies typically gate cPanel/WHM behind IP allow-lists or VPNs precisely because of this risk class, but small providers and self-managed VPS owners frequently expose port 2087 to the public internet. The Hacker News, The Register and Help Net Security all emphasised the months of pre-patch exploitation as the most concerning element — this was a true zero-day, not a panic over a freshly disclosed bug.
What This Means for Developers and Users
If you run cPanel or WHM yourself, patch immediately to the relevant fixed build for your release branch. Operators should additionally audit WHM accounts for unfamiliar users, review API token issuance, and check session-store directories for unusual file activity dating back to February. Customers of shared hosts should ask their provider in writing when CVE-2026-41940 was patched on the servers hosting their sites — and assume credential rotation is prudent if no clear answer comes back. End users of any site that runs on cPanel-managed shared hosting should change their account passwords and revoke long-lived API tokens.
What’s Next
cPanel’s public advisory promises a deeper post-mortem on its disclosure handling, after multiple outlets pressed on the two-week gap between watchTowr’s initial report and the vendor accepting that the bug was real. CISA is expected to add CVE-2026-41940 to the Known Exploited Vulnerabilities catalog within days, which will trigger a 21-day patch deadline for federal civilian agencies running cPanel-managed infrastructure. watchTowr Labs has indicated more research into related cPanel session-handling primitives is forthcoming.
Sources
Stay up to date with Doolpa
Subscribe to Newsletter →